Hidden GATT Bluetooth services
BR/EDR
BLE
In Bluetooth, a service refers to a specific functionality or feature that a device offers to other devices within a Bluetooth network. Each service is identified by a Universally Unique Identifier (UUID), and can be discovered and used by other Bluetooth devices that support that particular service.
In Bluetooth there are multiple ways to discover available services in a device. One of the mechanisms to perform this discovery is the Generic Attribute Profile or GATT and allows communication between devices through the exchange of attributes (data organized in a specific format).
It is mandatory GATT is present, it is important that it is correcly configured and that lists all the available services in the device. Failing to list a service in GATT does not prevent users from accesing it and does not secure it.
On the same topic, if a service is correctly secured, there is no need to hide it and correctly configuring GATT to list it will be in conformance with Bluetooth Specifications, allowing for better device interoperability.
Description
In order to check if there are hidden services it is important to perform a GATT discovery. This is an standard Bluetooth procedure that can be performed with standard bluetooth tools.
After having a list of available GATT services, it is needed to perform alternative ways of discovering Bluetooth services. This can include the following procedures:
- Capturing Bluetooth communications while operating the device to discover communications with previously unknown services.
- Performing bruteforce scans of services in a device.
- Performing service scans using different service discovery protocols such as the SDP if available.
If there are services hidden to the GATT service it is not correctly configured.
Related resources
To check this control, the following resources may be useful:
| ID | Description |
|---|---|
| BSAM-RES-04 | Bluetooth connections sniffing |
| BSAM-RES-05 | Capture of a Bluetooth connection |
Example case
The existence of hidden GATT services in a device with BLE connectivity will be tested. The tests will be carried out on a laptop. We will use Wireshark with BTVS (btvs.exe -Mode wireshark) to capture packets for analysis.
For this control it will be necessary to have python 3 installed. From a terminal it will be necessary to install the packages asyncio and bleak with the python installation wizard pip.
pip install asyncio.
pip install bleak.
To perform the search for Service exposed by GATT, the bleak script service_explorer.py will be used.
To run it it is necessary to know the MAC address of the target device and type the command:
python service_explorer.py --address XX:XX:XX:XX:XX:XX:XX:XX:XX >> gatt_explorer.txt.
A file (gatt_explorer.txt) with the traces generated by the service_explorer.py script is available and sorted for easy reading.
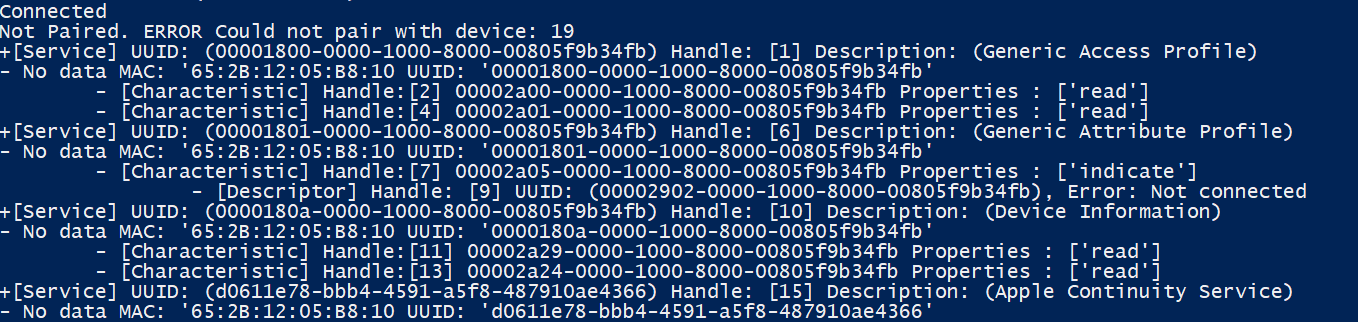
For each service (Service) there is one or more characteristics (Characteristic) containing one or more descriptors (Descriptor) and a value (Value). The services, characteristics and descriptors have two additional fields: the Handle and the UUID.
The Bluetooth driver internally lists the GATT services via the Handle or UUID field. The standard has limited, for a device, the number of services, features and descriptors to 65.535 (0xFFFF), equivalent to scrolling from value 1 to 65,535 in the Handle.
To check for hidden Service, a read request will be made with Scapy, or a similar tool like gatttool, for each Handle, depending on the response obtained for each query the Handle will exist or not. The possible cases of response to a read request, according to the ATT protocol, will allow to know if a Handle exists or not.
| Read Response | Handle Exists |
|---|---|
| Read Response | YES |
| Insufficient authorization error | YES |
| Insufficient authentication error | YES |
| Encryption key size too short error | YES |
| Insufficient encryption error | YES |
| Invalid Handle error | NO |
| Read not permitted error | YES |
Once you have the output of the two tools, compare the results and if there are Handle that are not listed with the bleak script, it means that it is a hidden service.
The check control FAIL when more existing Handle are found than discovered in the GATT scan.
