Forced bluetooth encryption
BR/EDR
BLE
The use of encryption in Bluetooth connections is optional.
The use of encryption mechanisms is highly recommended for access to any service that exposes sensitive information or allows unauthorized control of the device.
Not using encryption exposes the data on a connection to sniffing attacks and allows the use of attacks such as BIAS to extract data from the device without sharing or knowing the link key.
Description
To check if the use of encryption is required, the services that require confidentiality must first be classified.
Once the sensitive services have been listed according to their functionality, test connecting to them without having the link key.
This check will be considered successful if no data reading, access to functions or control of the device is allowed.
Related resources
To check this control, the following resources can be useful:
| ID | Description |
|---|---|
| BSAM-RES-04 | Bluetooth connections sniffing |
| BSAM-RES-05 | Capture of a Bluetooth connection |
| BSAM-RES-06 | Enabling debug mode on a Bluetooth controller |
| BSAM-RES-07 | Sending and receiving HCI messages |
| BSAM-RES-09 | Changing the attributes of a controller |
Other related documentation:
| ID | Description |
|---|---|
| Documentation | Bluetooth LE connection mode |
Example case
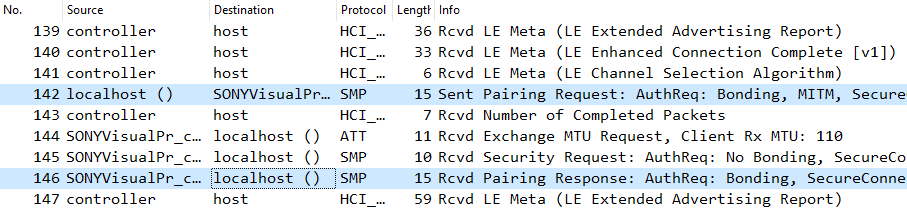
We will use Wireshark with BTVS (btvs.exe -Mode wireshark) (btvs.exe -Mode wireshark) to capture packets for analysis.
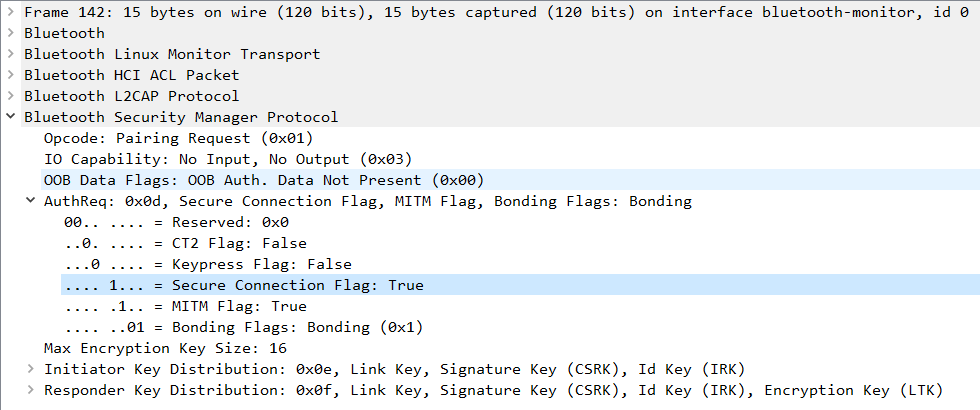
The pairing between Bluetooth headphones and a computer is then verified. Connection is requested through the Bluetooth device management application integrated into the computer’s operating system. In the Wireshark capture, the complete pairing process should be identifiable, starting with a Pairing Request command followed by the response command, Pairing Response, and concluding with the confirmation of pairing using the Pairing Confirm command.
In the Pairing Request command, the Secure Connections field should have the value 0x01.
In the Pairing Response command, the Secure Connections field should have the value 0x01.
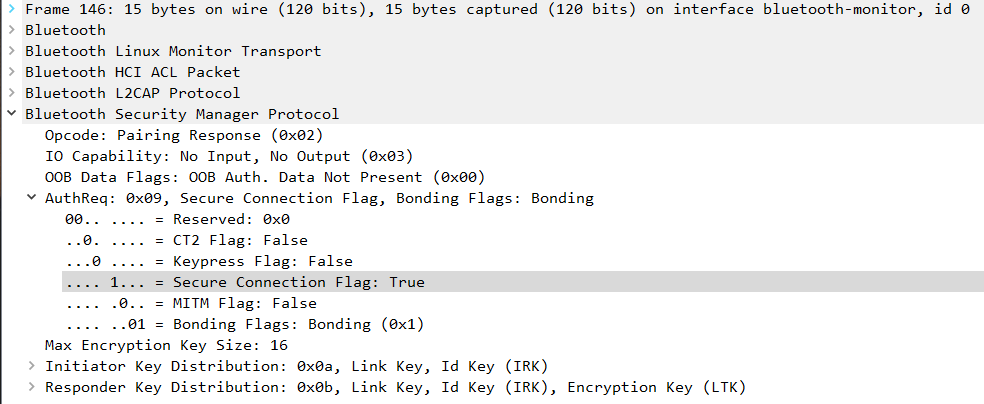
This process forces encryption between both devices, establishing a generation of secure keys.
If, in the messages of Pairing Request and Pairing Response immediately preceding the Pairing Confirm, the Secure Connections field has a value different from 0x01, this control will have failed.
The check control FAIL if either of the two devices has a Secure Connections field with a value of 0x00, and the connection is established.
