Threat intelligence
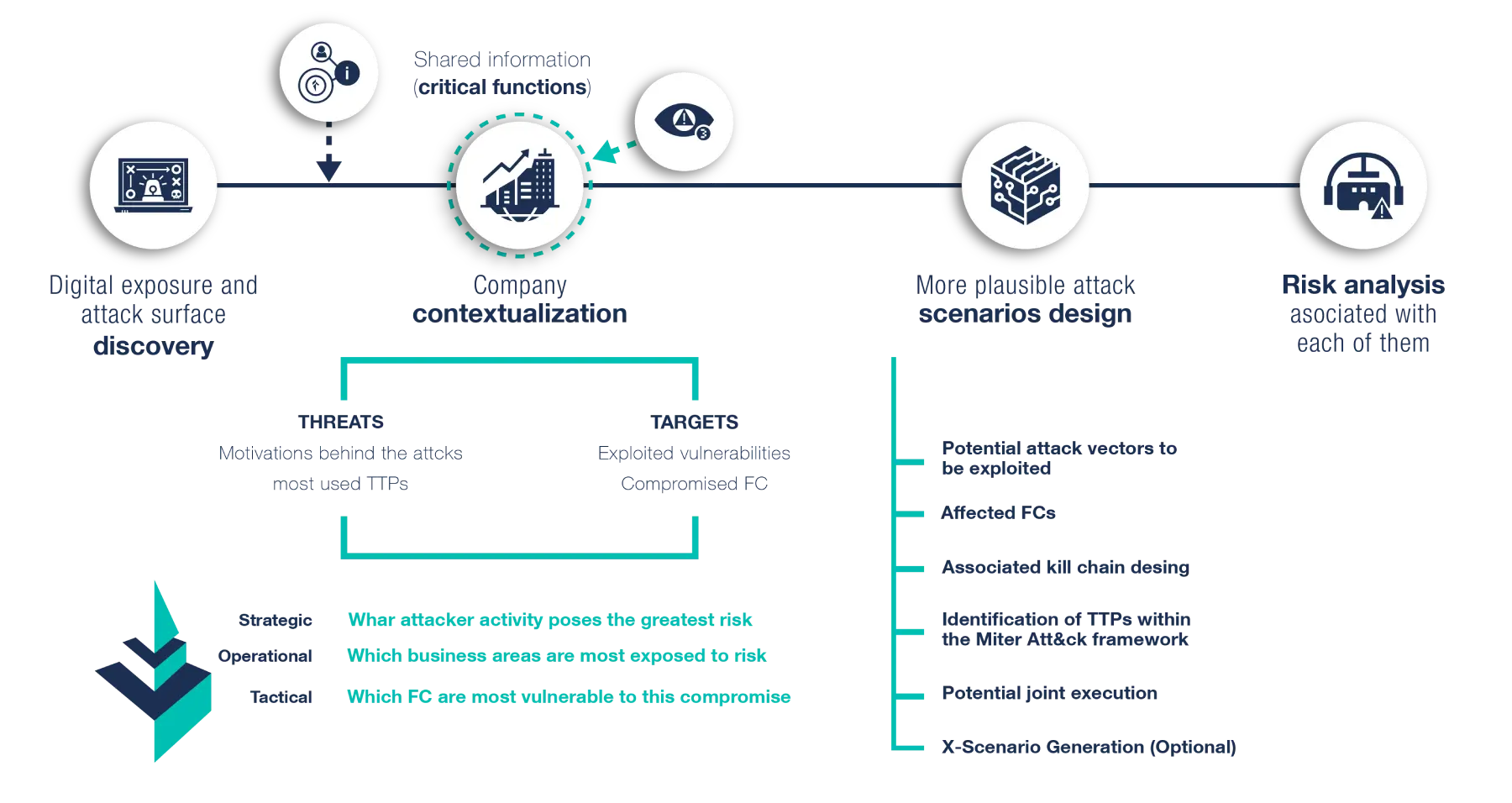
Targeted threat intelligence allows for the discovery of potential attack scenarios and risks, empowering organizations to strengthen their cyber defenses.
Fill in the form and we will call you back
Threat intelligence
We have developed our own analysis methodology, based on frameworks with proven results, which allows us to know the most plausible and realistic attack scenarios for each organisation, taking into account the peculiarity of its different lines of business and activities.
Highly valuable knowledge in diagnosing the level of cyber resilience and identifying areas for improvement in each case.
Modalities
Extensive experience in Threat intelligence services whose methodology, technological structure and solution approach has been entirely designed by Tarlogic.
Threat intelligence service

TIBER Threat Intelligence
Threat Intelligence Advisory
Others.
Threat intelligence objectives
Our extensive experience and managed knowledge of threats has allowed us to create high-value knowledge in the diagnosis of our customers, both of the organisation itself and of each of the functions that comprise it. This makes it possible to focus on prevention and protection of those areas most exposed to each risk.
Threat intelligence benefits
-
Provides an updated picture of the main threats to the sector.
-
Contributes to finding out the most relevant vulnerabilities of the organisation.
-
Highlights the critical functions most exposed to each identified cyberattack risk.
-
Facilitates the design of possible attack scenarios prioritised by their estimated degree of occurrence.
-
Guides future Red Team exercises independently.
-
Allows for the rapid adoption of preventive or, if necessary, mitigation measures.
-
Helps with decision making.