Vulnerabilities in headsets of top-brand allow eavesdropping on private conversations

Tarlogic presents research at RootedCON revealing how vulnerabilities in headsets can be exploited to eavesdrop on private conversations through the microphone of Bluetooth headsets
Tarlogic Security has demonstrated that it is possible to connect to a wireless headset without the user being aware of it, activate its microphone, and listen in on all conversations a person is having remotely. The Spanish cybersecurity company has developed BlueSpy, a solution that exploits vulnerabilities in headsets using Bluetooth technology to prove that it is possible to spy on companies and citizens and steal sensitive information such as intellectual property or financial data.
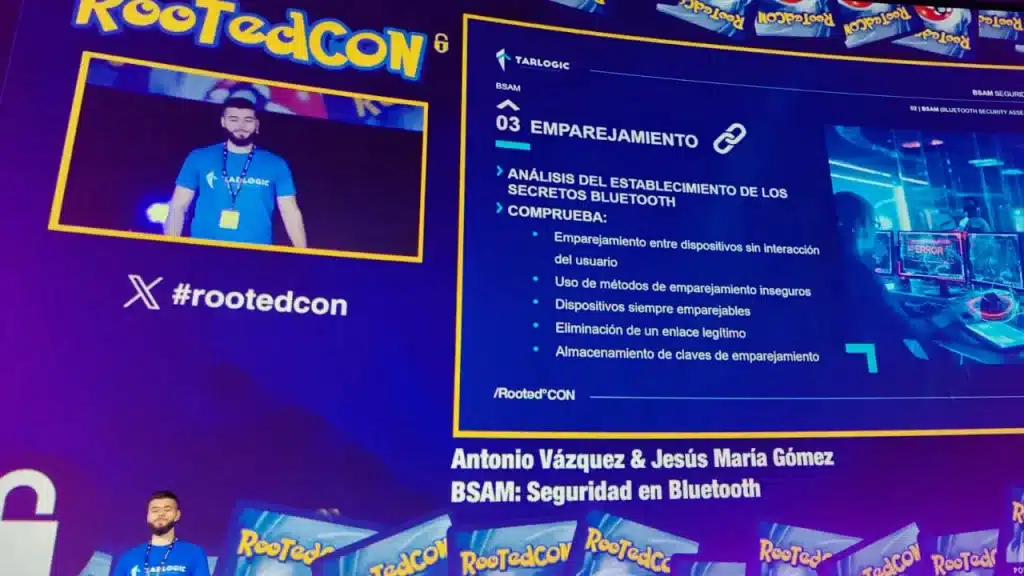
This new research, presented at RootedCON, the world’s largest Spanish-speaking cybersecurity conference, is part of the cybersecurity company’s commitment to highlighting Bluetooth security breaches. This communications standard is key to the operation of millions of everyday devices such as smartphones, computers, headsets, wireless keyboards and computers, smart locks, medical devices, and more.
Bluespy is publicly available
BlueSpy, the proof of concept designed by Tarlogic’s Innovation team, uses BSAM controls, the first Bluetooth security audit methodology, to detect vulnerabilities and connect to devices without their users being aware of them. The company’s professionals have been able to bypass wireless headsets from major manufacturers such as JBL and Samsung, activate their microphones, and listen to and record private conversations.
All the documentation to implement this proof of concept, which allows listening and recording conversations through Bluetooth headsets without users’ awareness, has been published on Tarlogic’s GitHub. In addition, the manufacturers whose devices have been analysed and in which vulnerabilities have been detected have been notified.
During their presentation at RootedCON, Antonio Vázquez Blanco and Jesús María Gómez Moreno, members of the Tarlogic Innovation team, explained the keys to a responsible disclosure project that seeks to focus on the dangers for companies and individuals arising from the fact that their everyday devices have security deficiencies in terms of Bluetooth connections.
Listening to and recording private conversations by exploiting vulnerabilities in headsets
Researchers at the cybersecurity company have analysed numerous wireless headsets developed by major global manufacturers and found that many devices have vulnerabilities that allow remote access to a user’s device without the user having to take any action to enable illegitimate access. To which we must add that:
- More and more people, especially professionals and business managers, are wearing their helmets all day long, even when they are not using them.
- Most headsets remain active all day long, often without the wearer being aware of it.
- Even when the headsets are put away in their case, they remain active for 3 or 4 minutes, waiting for the user to reconnect. So an attacker can take advantage of this time interval to connect to them and manage to listen in and record everything the victim does throughout the day.
As a result, malicious actors can exploit vulnerabilities in common Bluetooth devices such as wireless cases to turn them into microphones at their service. And the privacy of personal, professional, and business conversations can be compromised.
Spying on thousands of companies without breaking into them
The ability of malicious actors to access private conversations is a critical threat to businesses because it allows remote entry, turning corporate wireless headsets into microphones for industrial espionage activities.
Jesús María Gómez and Antonio Vázquez explained during their presentation at RootedCON that the risks faced by companies using insecure wireless headsets range from intellectual property theft, to access to financial information, conversations exposing customer information or management meetings where strategic issues are discussed.
Tarlogic Security’s proof of concept shows that criminal groups with the necessary know-how can carry out attacks against companies using vulnerabilities in Bluetooth technology as an attack vector.
Tarlogic’s researchers have also warned that it would also be possible to exploit vulnerabilities in headsets to listen to and record phone calls. This is because the latest versions of this standard support multiple active connections to the same device. This means that the victim and the attacker could be connected to the wireless headset at the same time, without the victim being aware of it. This potential attack further increases the risks faced by companies, their management, and professionals.
BSAM, a methodology at the service of manufacturers and cybersecurity experts
This project presented at RootedCON was carried out using BSAM (Bluetooth Security Assessment Methodology), a methodology developed by the Tarlogic Innovation team, which allows comprehensive security audits to detect weaknesses and vulnerabilities in devices that use Bluetooth connections.
The company’s researchers have used the 36 security controls that make up BSAM to find vulnerabilities in everyday devices and verify that it is possible to access them to:
- Carry out attacks against companies and citizens.
- Listen in on private conversations.
- Steal critical information.
- Access business secrets and even medical data.
To prevent such incidents, Bluetooth device manufacturers can use BSAM, an open and collaborative security verification guide that unifies the tests and validations that must be performed to assess Bluetooth security.

Dozens of Rooted Bluetooth devices raided
To demonstrate how the tool works and the importance of auditing Bluetooth devices, the Tarlogic team developed an application that was deployed during RootedCON to search for all kinds of devices with Bluetooth capabilities and try to access them to determine if they are vulnerable.
The result of this experiment was made public during the presentation by Jesús María Gómez and Antonio Vázquez:
- Between 9 am and Thursday afternoon (the start of RootedCON), dozens of passcodes were obtained to connect to these devices. Among the gadgets targeted in the mock attack were smart bracelets, headphones, smart TVs, and even a phone and a computer.
Tarlogic researchers showed the audience the passwords obtained during the test. These random passwords are very important because they allow a device to connect to another device via Bluetooth, associating with the MAC address of that device, so that it is possible to connect automatically in the future.
What could happen if malicious actors got hold of a passkey and knew the MAC address associated with it? They could access a Bluetooth device from a third party without attracting the victim’s attention, which opens the door for experienced and trained criminals to carry out multiple attacks to steal information.
Tarlogic is a company committed to the protection of companies and citizens
The tool presented today and the development of the first methodology for auditing Bluetooth devices follow in the wake of other projects of the Tarlogic Innovation team around the security of this technology, such as the design of Bluetrust. This attack technique makes it possible to discover trust relationships between Bluetooth devices and to infer personal data about the people who use them and the companies they work for.
Tarlogic Security is thus consolidating its position as a global benchmark for Bluetooth security and the effort to strengthen the protection mechanisms of millions of key devices for the day-to-day life of companies and homes.
Over more than a decade, Tarlogic Security has become a leading cybersecurity company, providing a wide range of cybersecurity services, cyberintelligence, or audit of defensive and offensive services to numerous listed companies and multinationals.
