Counter-Phishing: Anticipating the criminals
Table of Contents
Generally speaking, we estimate risks based on our ability to protect ourselves against the actions that trigger them. This capacity increases the more knowledge we have of the event itself. In the field of cybersecurity, cyber-intelligence services such as Counter-Phishing have started from this premise and have become indispensable allies to knowing in detail the techniques, procedures, actors, and technology used behind phishing, a constantly growing threat.
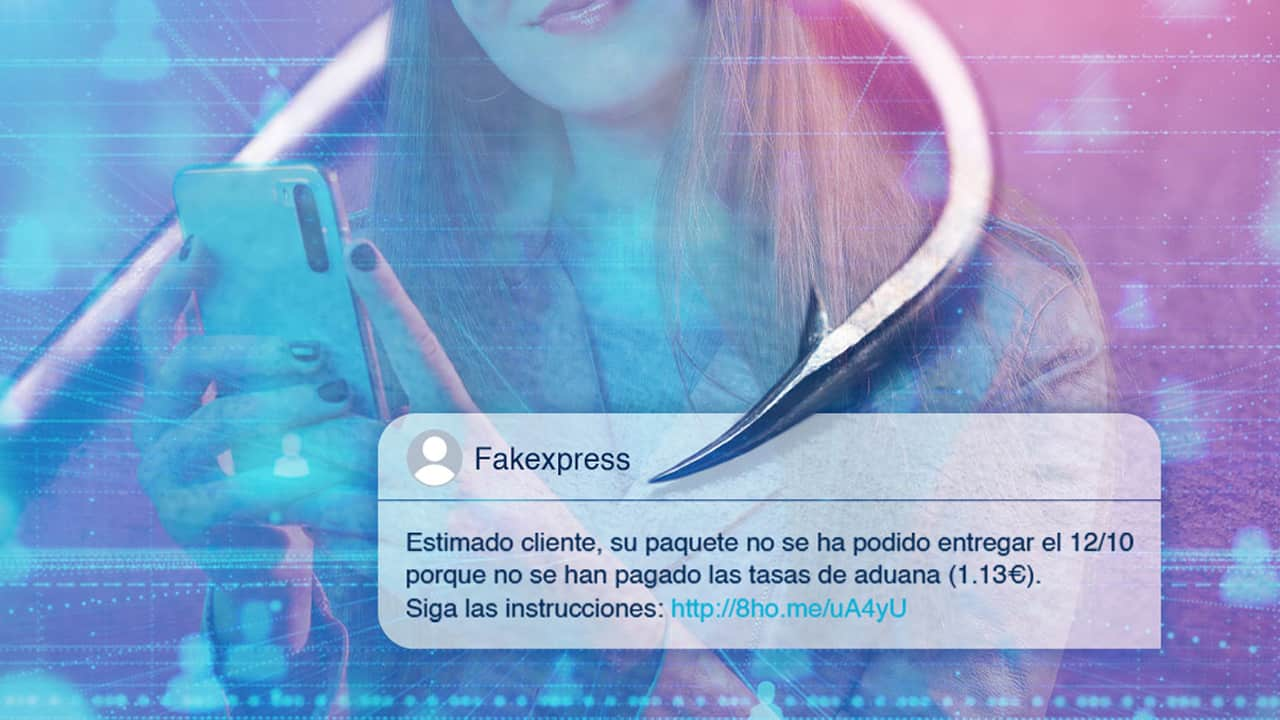
Phishing campaigns and their different variants such as vishing or smishing have become a headache for companies and institutions around the world, especially for entities in the financial sector. Through fraudulent e-mails, phone calls, and SMS, criminals seek to deceive mainly end users by impersonating organizations or third parties.
As a cross-cutting variable underlying these actions is an element that is as common as it is key: taking advantage of the emotional, social or economic, and therefore personal, circumstances to which people are exposed. And it is precisely this factor, the human factor, that is the pillar that must guide the construction of prevention capabilities for orchestrated campaigns under social engineering actions.
In other words, the success of the fight against fraud that a Counter-Phishing activity must ensure cannot and must not rely on software or automated «solutions». Human behavior must be analyzed and prevented from a human perspective.
The constant evolution of phishing campaigns
Origin
The use of social engineering dates back to the late 1800s, but it was not until the spread of Nazism that its use was mainly attributed to deception and social manipulation, an issue that is still widely debated today.
Phishing actions, as we know them today, gained relevance in the 90s, having acquired an exponential generalization in the last two years. In particular, those affecting the financial sector, as organizations such as CCN-CERT and the banks themselves have shown.
Just a few weeks ago, following an incident involving an information leak at Revolut, a leading Fintech in the online banking sector, attackers managed to steal data from more than 20,000 users and triggered a phishing campaign targeting them.
This virality is not only resulting in the existence of more phishing campaigns but also a constant evolution of the tactics, techniques, and procedures used by the attackers.
Campaign sophistication
Although crude scams that have been deployed under precarious structures persist, sophisticated campaigns whose detection is becoming more and more complex for large sectors of the population, continue to grow. Messages, emails, calls, and the fraud formats used are as broad as they are varied… the communication channels we have incorporated into our daily lives.
In mid-September, the National Police announced the dismantling of a criminal gang that was able to steal 600,000 euros by implementing a complex and sophisticated phishing campaign. The criminals designed a malicious website that looked like a bank and managed to position it in the heat map of a search engine. Bank customers entered their data on the fraudulent page. The criminals then used this data to access their online banking and to obtain a duplicate of the victims’ SIM cards. Once they had them, they logged back into the banking app, made money transfers, and applied for immediate micro-credits, validating all actions thanks to the duplicate SIM.
Follow the money and the exploitation of human psychology, the variables behind phishing
How do phishing campaigns succeed? Several variables come into play. From the aforementioned increasing sophistication of the attacks to the criminals’ ability to get close to where the money is, to the workings of the human psyche itself.
As Deep Throat told the seasoned journalists who uncovered Watergate in All the President’s Men, the key is «follow the money». Criminals have extensive knowledge of how banks operate and what data financial companies’ apps and platforms demand. Some phishing campaigns bet directly on impersonating banks. Others, on the other hand, are more subtle and intricate and use less direct means to achieve their goals and avoid raising suspicions among victims and organizations.
In turn, perpetrators also use the mechanisms of human psychology to their advantage. The greater their knowledge of how people respond to certain situations, the more likely it is that victims will fall for the deception. In this regard, phishing campaigns must be able to generate trust in the victims. To do so, they must keep a semblance of reality so that users are not suspicious of the danger they are in. Luckily for criminals, many people are like Blanche Dubois, the protagonist of A Streetcar Named Desire, and trust «in the kindness of strangers».
More targeted threats using new technologies
In addition to the obvious increase in phishing attacks, two other key issues underlie this fraud.
On the one hand, there is the emergence of new types of phishing attacks that take advantage of new services and technologies to increase the effectiveness of the attacks, while at the same time perfecting, standardizing, or making the classic ones more complex.
On the other hand, the use of spearphishing techniques is limited to larger and more targeted fraud campaigns against their victims, combining social engineering techniques such as phishing with the implementation of malware or ransomware.
In this context, the increase in information leaks, as well as the digital overexposure of users and companies, are ideal components for threat actors to develop their campaigns with a higher probability of success.
A seemingly legitimate email or phone call can open the door to viruses that take control of devices, applications, or bank accounts of individuals and companies.
Phishing + malware: A dangerous dynamic duo
At the same time, more intricate or subtle types of phishing have come to light, which does not involve sending direct communications and redirecting to malicious web pages, but, for example, downloading fraudulent mobile applications through which to install malware on devices.
This is the case of Xenomorph, a virus hidden behind a legitimate app that could be downloaded from the Play Store to clean the mobile system. Once the app was downloaded, the malware took control of the device with a clear end goal: to take over bank accounts by hacking legitimate banking apps.
This large-scale fraud allows us to observe the level of danger of campaigns that combine the art of human deception with the most innovative technology. At the same time, it highlights the value of companies in general, and banks in particular, betting on advanced fraud investigation and analysis services such as Counter-Phishing.
To take control of banking applications, malicious agents not only deployed malware but also combined this action with the sending of attacks via SMS. In doing so, they sought to obtain all the necessary access permissions. In this way, they were able to complete a large-scale economic fraud.
Along the same lines, a browser-in-the-browser phishing campaign has been able to steal Steam accounts, a leading video game platform, using malware that clones the browser, making users believe that they are accessing Steam when they enter their passwords, when in fact they are giving them to the criminals.
Consequences and Liability
The new types of phishing and their combination with other techniques in the development of refined and complex attacks paint a confusing picture in which users must tread carefully and companies must redouble their efforts to anticipate the strategies of criminals.
Otherwise, both individuals and organizations will have to face the consequences of fraudulent campaigns.
The effects of a successful bank phishing attack impact the finances of customers, as well as the reputation and business of the banks whose identities and applications have been impersonated and breached.
Given the level of impact of security incidents linked to phishing, it is relevant to elucidate where the responsibility lies when such incidents materialize.
To this end, it is relevant to classify the different types of banking fraud, depending on who initiates the fraudulent payment:
- Unauthorized persons.
- Authorized persons.
If the payment is made by unauthorized persons who have taken the credentials of the persons or businesses that own the bank account, the financial entity must return the amount of money stolen. Since RD-law 19/2018 on payment services obliges banks to have the necessary security measures in place to guarantee the identity of their customers and safeguard the authentication process of transactions.
Only when the customer has committed gross negligence will banking entities be able to evade their responsibility in the face of frauds such as those we have been describing throughout the article.
Therefore, financial institutions must anticipate the evolution of these frauds and thus avoid the economic, legal, and reputational consequences associated with these security incidents.
Human and technical factors that make prevention difficult
Prevention of this type of attack involves two complementary issues. On the one hand, organizations and citizens need to be aware of the dangers of social engineering attacks. A user who opens a link that arrives in an e-mail can end up being the victim of an economic fraud that can have serious repercussions on his or her life.
Companies in general, and banks in particular, must be aware of the risks of cyber-attacks and always act with caution and prudence.
Beyond this human factor, the technical aspect is fundamental when it comes to preventing the launch and success of phishing campaigns. Professionals dedicated to fraud investigation and analysis, providing services such as Counter-Phishing, have to deal with increasingly complex and sophisticated strategies and techniques, which incorporate constant technological advances and innovations, making it impossible to deal with a threat of this nature from an immobile vision, lacking investment in innovation, however extensive it may be.
Examples of parameters used to make phishing investigation and prevention more difficult
In many cases, the conditions of access to the phishing sites themselves are very restrictive as a way to avoid documenting the appropriate abuse of content to request the closure of these domains, applying parameters such as:
- Redirects are programmed using shortener services to make detection of the malicious site more difficult.
- Access to the site is usually controlled to allow access only from mobile devices so that it is often not possible to view the phishing campaign from a browser on a PC. When attempting to do so, in most cases, the server shows the domain as offline, displays an HTML error message, or redirects to a third legitimate domain.
- The geographical location of the access is also established as an access criterion, often not allowing interaction with these domains with IPs not associated with the region in question.
- Once this impediment has been circumvented or accessed from a mobile device, the fraudulent site registers the access pattern and, in many cases, only allows a single phishing login.
- Combinations of hostings in different countries whose fraud prevention policies are laxer.
- The operation of the same phishing case changes over time, as those responsible for it activate and deactivate different data request functionalities, depending on the success of the phishing campaign itself.
- Campaigns are deployed very quickly, an issue that has been encouraged by the use of kits as a service, which can often be acquired at a low cost and deployed by less advanced actors.
- Linked to the latter, in many cases a first domain is created to impersonate a specific entity, which is then associated with multiple subdomains relating to third parties, thus providing a high degree of flexibility in the agile creation of cases.
- Sending fraudulent URLs via SMS instead of email helps cyber criminals to avoid security mechanisms such as email anti-spam, which are implemented by organizations and email services such as Google or Microsoft.
- In this context, the fact that users generally do not have security solutions on their mobile devices increases the degree of success of these actions.
- The fact that malicious actors are aware of the adoption of countermeasures to prevent their activity also makes them invest in technologies and the use of services such as the Cloudflare CDN to hide their infrastructure and protect themselves from detection by third parties.
Counter-Phishing: A crucial service for preventing attacks
In order not only to detect but also to combat the growing wave of phishing that stalks the financial system – and its users – Tarlogic launched a Counter-Phishing service at the beginning of 2022 that is proving to be highly effective in prevention.
Our Cyberintelligence team, with extensive experience in the investigation and analysis of fraud, has taken advantage of the knowledge acquired over the years from the main players in this sector to address, from a technical and human perspective, the neutralization of this type of action.
As a result, our Counter-Phishing service is based, among others, on 10 strategic actions:
- Early detection of campaigns and their associated domains, and their detailed analysis.
- Incorporation into our database of behaviors and patterns that can be used for the detection of illegitimate uses.
- Deployment of autonomously executed techniques and countermeasures, specifically targeting each phishing campaign when it is triggered.
- Use of a distributed response infrastructure in different geographical areas of the world.
- Continuous research and adaptation of response capabilities to the tactics, techniques, and procedures employed by malicious actors.
- Monitoring of restarts of activity, changes of structure, or new modes of action within the framework of existing campaigns.
- Strengthening of the takedown in each case.
- Personalized assistance in designing the internal prevention policies of organizations, as well as their external recommendations to users.
- Continuous updating of the work process to the challenges presented, understanding that research and innovation must be constant.
- Micro and macro analysis of the trends that show these attacks in the sector.
This article is part of a series of articles about Digital Fraud
- Counter-Phishing: Anticipating the criminals
- Stolen accounts, IPTV apps and pirate platforms: how audiovisual fraud work
- Hacking of social network accounts and creation of fake profiles: No one is safe
- SIM swapping, when your phone, and your money, are out in the open
- How do cybercriminals carry out fraud in the tourism sector?
- Black Friday alert! 10 keys to cyber-attacks against e-commerce and their customers
- Digital asset theft: Easy money for cybercriminals
- Cryptocurrency fraud, social media hacking, malware, and AI
- A wave of digital fraud to citizens
- 10 tips to avoid cyber-attacks on Black Friday