Risks of hardware design
Table of Contents
This article presents a current problem that goes unnoticed nowadays, the risks of hardware design by using obsolete components or components about to end their life cycle.
Hardware design, keys and phases
The hardware design of a device is a long and very complex process through which the physical design of the device is made. For the device to be functional, it is necessary to complement the hardware design with software that governs and regulates the hardware.
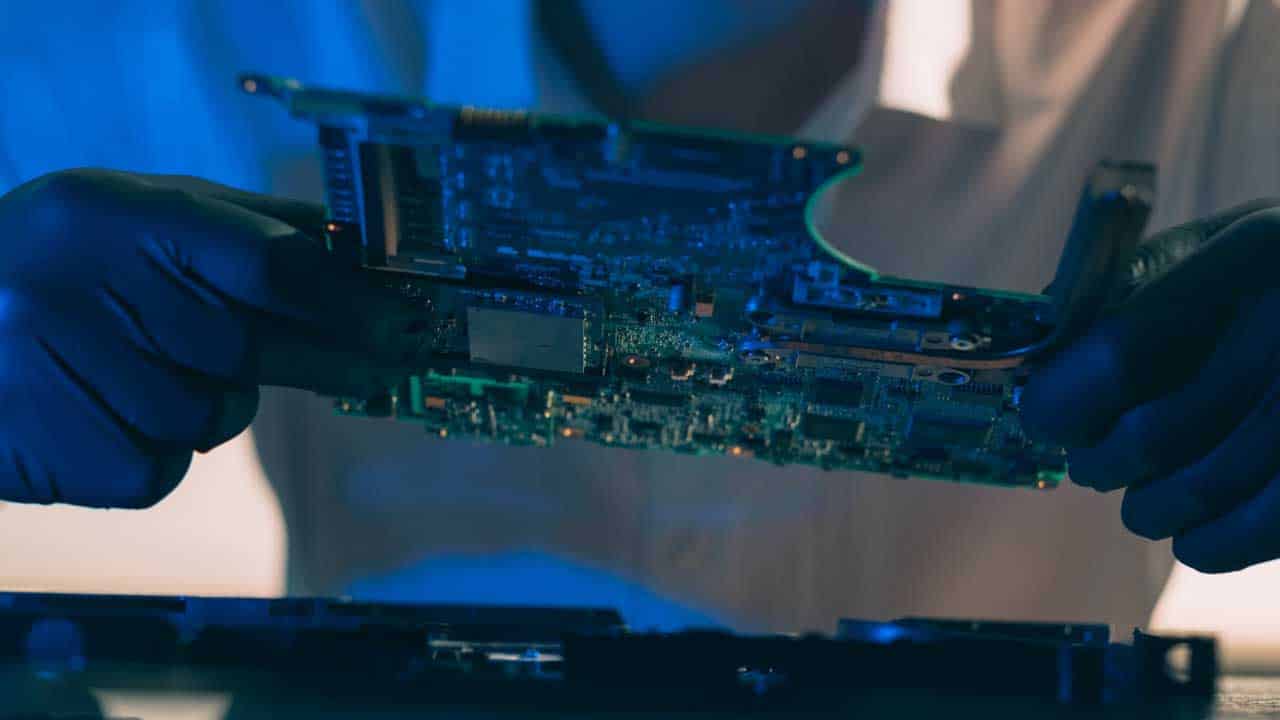
Hardware designs are made on what in electronics are called PCBs (printed circuit boards). These boards are made of a non-conductive material and on them are defined paths (tracks) of conductive material (usually copper) that allow interconnecting the different components of the design. Generally, PCBs are divided into layers to facilitate the interconnection between components and to prevent the tracks from crossing. The outer layers are usually grounded to isolate the system from external interference.
The PCB design process can be separated into three fundamental phases: device definition or scope; form factor and industrial design; and component selection and PCB layout.
1. Device functionality
During the first phase of the device development process, the expected functionality of the device and the working environment in which it will be used must be defined. Based on these concepts, the conditions (standards and requirements) to which the device to be manufactured must be subjected are determined.
There is a set of regulations that are common to all devices and are related to their safety. These regulations include safe designs to prevent interference with other devices (EMI / EMC) or electrical isolation to avoid possible overvoltage. Depending on the application of the device, stronger restrictions may apply.
Two practical examples are proposed below to help visualize these types of restrictions: a toaster and an industrial sensor.
The toaster would be classified as a generic, domestic device that must comply with the most standard constraints such as not interfering with other devices (e.g., coffee maker, refrigerator…) and being electrically safe. On the other hand, the industrial sensor will be subject to stronger restrictions.
Suppose, for example, that you want to design an altimeter for an aircraft or a sensor for a nuclear power plant. These devices, in addition to the basic safety requirements, will have to comply with regulations specific to their operating or working environment (high vibrations, radiation levels…).
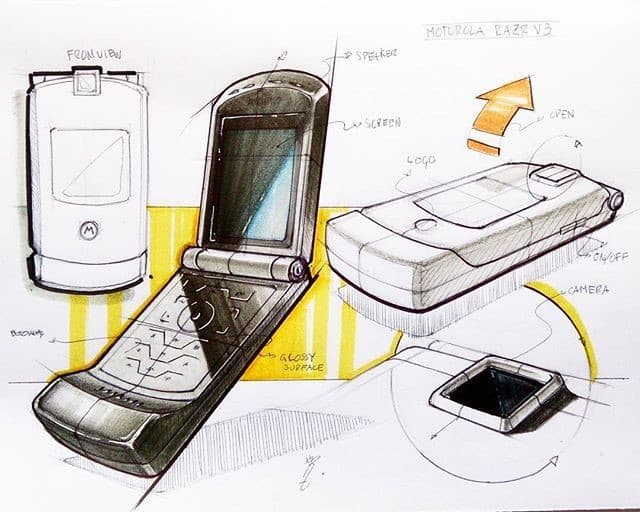
2. Device aesthetics
The second design phase focuses on the form factor of the device. In this design stage, the final aesthetics of the device must be considered, as well as the intended use of the device.
If you take as a reference the design of a smartphone you will have to consider the size, weight, color … as well as another set of measures and parameters such as the type of screen, the size of the battery, the camera sensor. All these factors influence the perception of the end consumer and severely impact the brand image of the company (both positively and negatively).
The size of the device is a determining criterion as it conditions both the size of the components and the number of components that can be included in the design.
A few years ago, Samsung suffered a significant depreciation of its brand due to a design flaw in one of its flagship products: the Galaxy Note. As a result of a design flaw, the device’s battery could not expand and contract freely, causing it to explode at some point. While it is true that this example does not correspond to a design flaw at the electronic level, it exemplifies very well the importance of this phase during product development.
3. Component selection
In the third phase, components are selected that meet both the performance requirements and the industrial design requirements of the device.
Depending on production volumes, components can be purchased exclusively for a device or generic products can be purchased and included in our design. Currently, most companies make use of third-party components to manufacture their own products.
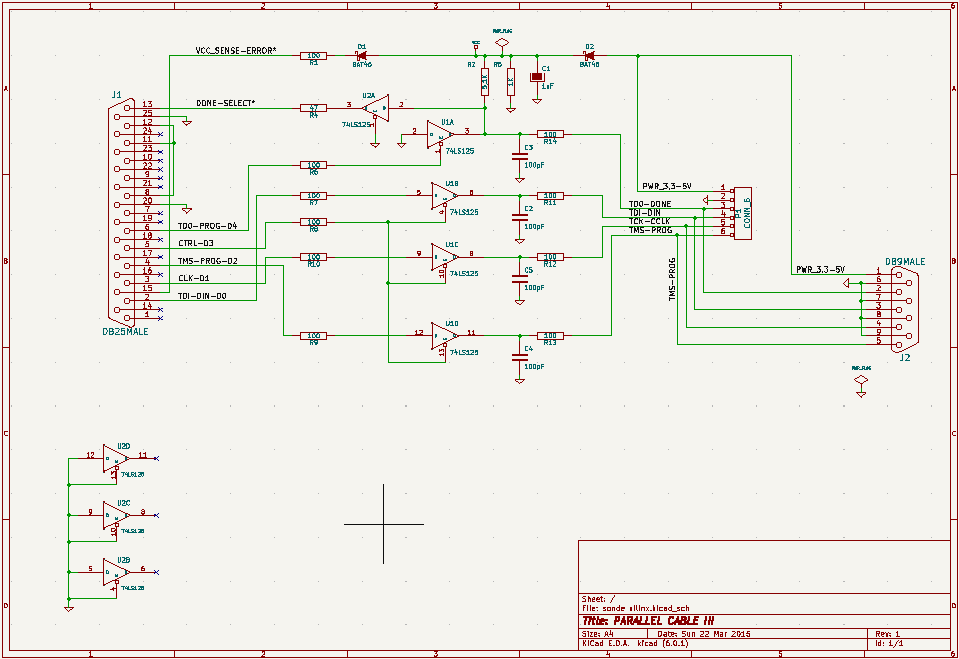
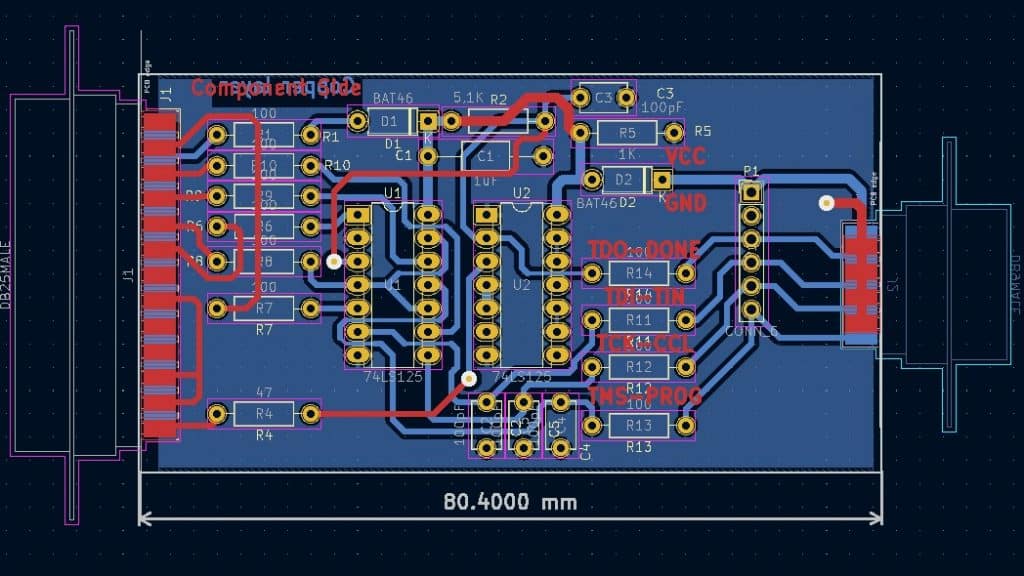
Once the components have been selected, we proceed to the PCB design itself. Specialized hardware design programs such as Altium or KiCad are available for this PCB design process. These specific programs are an indispensable aid for the electronic engineer since they allow the design of the schematics, the layout of the components on the board and the connections between them (traces/tracks).
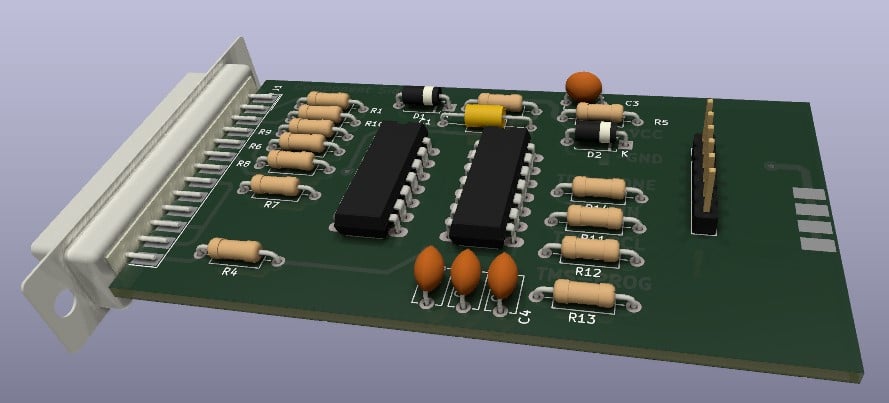
Another interesting feature of this type of tools is that they allow us to work with component libraries. A footprint is associated to each component, which is nothing more than a virtual representation of the component packaging.
During PCB design, these footprints are arranged along the board so that during PCB assembly the components are soldered on top of their respective footprints. Thanks to tools such as Altium or KiCad we can have numerous libraries of components or create our own footprints in case there are no default ones for a specific type of component.
The component selection process is quite laborious and requires deep research by the electronic engineer.
Due to the large number of components on the market, it is necessary to identify the type of components required for the PCB to be designed and, for each of them, the datasheet of the components must be consulted.
Component properties
During the study of the datasheet, the form factor of the component (size, type of footprint…) as well as other properties of the component (operating voltage, decoupling capacitors, load impedances…) are checked. If different alternatives are available, e.g., different components performing the same functionality, the following criteria must be applied to discriminate the right choice: price, availability, and life cycle of the component.
Currently, due to the device stock crisis (commonly referred to as the “silicon crisis”), availability and price have positioned themselves as two determining factors in the choice of components.
On the other hand, the life cycle of a component is defined as a manufacturer’s estimate of the time it considers necessary to cushion manufacturing costs and make a profit on the sale of the component. Once this lifetime is exceeded, the manufacturer withdraws the component and releases a new version.
In simple components such as resistors or capacitors, the life cycle has a relatively low impact on the device design since replacing these components is very simple as they are so standardized. However, replacing more specific and complex integrated components is somewhat more complicated because it may require a total hardware redesign if the footprint (shape) or any of the properties of the component change.
It’s important to keep in mind that life cycles are not only related to component improvement over time but also to supply and demand among manufacturers. If a manufacturer detects that one of its products is selling less than a competitor’s, it will try to resemble the competitor’s product by modifying the component’s properties and shortening its lifetime. These modifications can be transparent to our design or have a very negative impact on it.
To facilitate the selection of components, you can make use of the main distributors’ websites or use specific tools such as Octopart to search for them.
Risks of hardware design with obsolete components
The main advantage of designing with older components is that the physical behavior of the components is well known, reducing the risk of possible hardware errors. On the other hand, in terms of software, it is much more likely that new vulnerabilities will appear in components with a longer lifetime, since it is more likely that there will be more researchers focusing on them over time.
The main problems of designing with older components are stock-outs and unpatched vulnerabilities. Regarding stock-outs, not having a critical component available may mean having to redesign the entire product. The latter is especially important for repair and maintenance work, where little else can be done without the specific component.
As far as vulnerabilities are concerned, these tend to be more software-related than hardware-related, so if the device can be updated in some way, we would not have these problems. The difficulty here is that many systems (e.g., IoT nodes) do not have update mechanisms available. Finally, in the case of hardware vulnerabilities, time is a bad ally, and the only possible solution is to replace the component with another unaffected one (in this case, redesigning the system).
Hardware design risks with new components
Designing with new components has the advantage that the supply of these components is closely aligned with the expected lifetime of the device we are developing. The problem with these components is that because they are so new, it is unknown how they will behave in the long term and whether they have any associated vulnerabilities.
The potential vulnerabilities associated with new components can be classified into hardware or firmware bugs.
Hardware bugs have a very high impact and require a new hardware version to be released for remediation. They are usually related to design faults related to the operation of an individual component or the board in general (errors with impedance calculation, forgetting to place decoupling capacitors…).
Firmware errors are usually solved by the manufacturer of the integrated board, by updating the internal software of the board. It is common that the batteries of some communication protocol fail and do not allow certain connection modes or fluctuations in the transmission speed. A common example of this type of failure that has been around for a long time is the I2C bus expander.
Design alerts due to hardware obsolescence
All components have program obsolescence and sooner or later disappear from the market. As discussed throughout this article, the impact of the disappearance of a given component can be trivial or critical.
If the replacement of the component with the new version can be included in the hardware design, the impact is minimal, and the solution is trivial. However, if the components are modified (form factor, properties…) or if they disappear, the impact is critical, and the device has to be redesigned.
Tarlogic’s Innovation team recommends to always try to work with updated components or components with long life cycles to avoid security problems or shortages in the future.
Regarding security issues, it has been detected that many manufacturers release products with old hardware components that incorporate, for example, Bluetooth 5.0. There are currently many Bluetooth vulnerabilities affecting this version. Therefore, Tarlogic’s Innovation team recommends using more up-to-date components that incorporate more up-to-date Bluetooth versions (5.2) to mitigate this type of risk.
Regarding the risks arising from supply shortages, because of the silicon crisis, many manufacturers are unable to produce new devices because they do not have all the necessary components for their manufacture. An example of this can be found in video game consoles, where large companies such as Sony or Microsoft are unable to manufacture the PS5 or the Xbox.
In the case of more modest companies, a supply problem can mean that their main source of income disappears, and they may even go bankrupt as a result.
Future/present hardware design risks
Designing with obsolete hardware does not necessarily mean a handicap for the customer if he is aware of it and is willing to assume the risks arising from this circumstance.
Tarlogic’s Innovation Department has classified the potential risks into three families:People’s safety risk.
- Equipment’s safety risk.
- Information security risk.
- Security risks to people are defined as all those risks that can trigger harm to people.
An example of such a risk could be launching an attack to violently turn up the volume on a vulnerable Bluetooth 4.1 speaker, causing a perforated eardrum to listeners.
Security risks to equipment are those that can trigger a defect in the operation of the device that cause that device (or others that depend on it) to suffer damage that results in harm.
The main problem of this type of risks is to identify the source or vector of entry, and the impact of the same. From the Tarlogic’s Innovation team, we are continuously studying new technologies, communications and use cases of devices implemented in the market to identify preventively this type of risks.
Finally, information security risks are those that can trigger a security breach and/or information theft. In many cases, the attack vector for this type of risk is associated with old hardware components. Therefore, the Tarlogic’s Innovation team warns that using old and vulnerable hardware in new devices is a bad design practice.
Hardware design findings
In conclusion, Tarlogic’s Innovation team recommends that all decisions taken during the design process should be made with full knowledge of the facts.
As discussed in the article, there are risks both when using obsolete components (out of stock, known vulnerabilities, end-of-life cycle…) and new ones (possible new vulnerabilities, zero-day).
The ideal is to work with components that, on the one hand, are relatively new and have a life cycle like the one we want to offer with the device; and, on the other hand, that have been properly audited and have no vulnerabilities associated with them. Unfortunately, matching both criteria is not an easy task and in most cases a compromise between benefit and risk has to be made.
It is expected that, soon with the proliferation of IoT devices, secure hardware design will position itself as a critical and in-demand element in the cybersecurity paradigm. Connecting a vulnerable device to a network (home or work) poses a very high risk as it acts as a gateway for more complex attacks.
Discover our work and cybersecurity services at www.tarlogic.com