Tarlogic presents research on the market for fake data leaks
• Tarlogic’s Cyberintelligence team presents research at RootedCON on the underground economy surrounding the generation of obsolete, manipulated, or completely fake data leaks
• Fake leaks are also a tool for extortion, targeted disinformation, and narrative manipulation
In recent months, public administrations such as the Ministry of Finance and the Tax Agency, energy companies, technology multinationals such as Meta and NordVPN, and textile companies such as Canada Goose have denied having suffered data leaks publicized in forums and disseminated on blogs and social networks. These cases are not anecdotal. Tarlogic Security’s Cyber Intelligence Department has conducted research into the global business of selling obsolete, manipulated, or completely false data as new or recently stolen information.
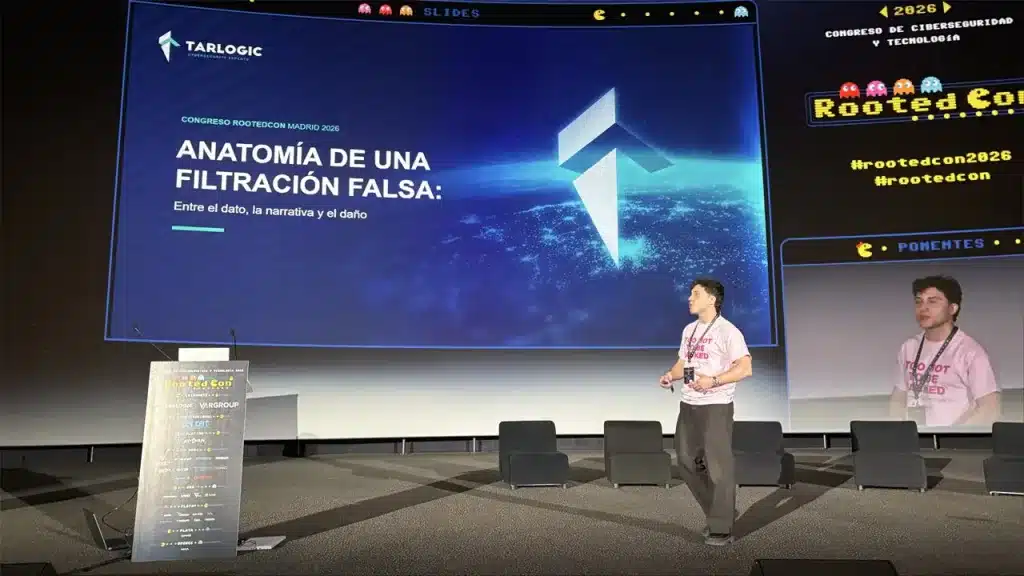
The results of this investigation were just presented by Alejandro Julián Pachés, Senior Threat Intelligence Analyst at Tarlogic, at RootedCON, the largest Spanish-language cybersecurity event.
The Tarlogic team infiltrated forums where fake leaks are traded and disseminated to understand how information is prepared to appear credible and to determine the motivations of the actors operating in this market.
In addition, they analyzed how the image of companies and institutions accused of suffering leaks that did not occur is damaged, and how organizations should manage these crises.
Leak-as-a-Service. A global market for fake leaks
In recent years, both companies and public administrations have strengthened their security strategies to prevent data breaches, particularly the leakage of sensitive customer or citizen data.
Given this scenario, some criminal groups have started operating a global market for fake leaks, accessible through forums, where users can purchase fake leaks, as certified by Tarlogic researchers after interacting with multiple actors who benefit from this illegal business.
Using a Leak-as-a-Service model, cybercriminals sell leaked company data. However, the leaks are not real; the data is old, compiled from past leaks, manipulated, or synthetically generated to appear credible.
Thanks to this model, attackers without the technical knowledge or resources to compromise an organization’s security can obtain data that appears to support the existence of leaks.
In addition, the Cyberintelligence team at Tarlogic Security has detected that these forums not only sell fake leaks but also allow users to create blogs and website posts to publicize leaks that have not occurred.
This market for fake leaks represents a paradigm shift. What matters now is no longer the data, but the ability to spread the word about a leak that has not occurred, thereby causing extensive reputational damage.
The economic objective would be the main motivation
Criminal groups that opt for the Leak-as-a-Service model seek to profit directly by selling leaks to third parties via forums.
The actors who acquire the leaks can use them to:
- Extort companies that have supposedly been successfully attacked, threatening to make public information about their customers, partners, or employees.
- Spread false information to damage a company’s or administration’s reputation, impose a narrative of the organization’s cybersecurity strategy’s weakness, and misinform, generating a sense of alarm among the public. With regard to the latter issue, we must bear in mind that citizens and customers may fear that their personal data will be used to commit fraud against them.
Similarly, as Alejandro Julián Pachés pointed out during his presentation, we must not lose sight of the fact that some actors fabricate false data leaks to gain notoriety and credibility in forums where malicious actors interact. This is because claiming that a large company or government has been compromised can lead to significant exposure.
Managing false incidents accurately and quickly: a major challenge for organizations
Dealing with a security breach is a complex task, but incident analysis and response teams are prepared for it, and companies have plans in place to deal with these situations. But… how do you manage a crisis in which security has not been compromised?
In this scenario, companies are forced to activate their crisis committees and make decisions that have a major impact on security and image, as well as on their legal obligations. We must not lose sight of the fact that if a personal data breach has occurred, it is mandatory to inform the Spanish Data Protection Agency and, in many cases, the individuals who may have been affected.
Based on the Tarlogic team’s experience managing this type of incident, the research presented at RootedCON concludes that a detailed analysis of the event is essential to determine whether it is a false alarm.
This involves analyzing the author who disclosed the leak, their history, associated profiles, communication language, similar leak patterns, the consistency of the allegedly exfiltrated data, patterns of disclosure, and interactions with them and their environment across different forums, etc. This activity cannot be relegated to automated tools.
Likewise, the crisis committees of companies and institutions must be prepared to manage false incidents by incorporating such scenarios into their crisis management and communication plans.
Tarlogic, a leading company in the investigation of threats against businesses
This research on the market for false data leaks and their impact on companies is part of Tarlogic’s ongoing work in the Cyber Intelligence Area to fight fraud and threats to the productive fabric.
Over the last few years, the company’s Threat Intelligence specialists have gathered information on threats in each economic sector, designed potential attack scenarios, and contributed to the adoption of preventive measures and decision-making in cybersecurity to prevent incidents or minimize their impact.
Since its inception more than a decade ago, Tarlogic Security has established itself as a leading threat research firm. The company currently provides cybersecurity, cyber intelligence, and defensive and offensive service-auditing in Europe and the United States, and works with multinationals and listed companies across a wide range of sectors.
