BSAM Checker
Automatically audit the security of Bluetooth devices and detect vulnerabilities.
Request more information
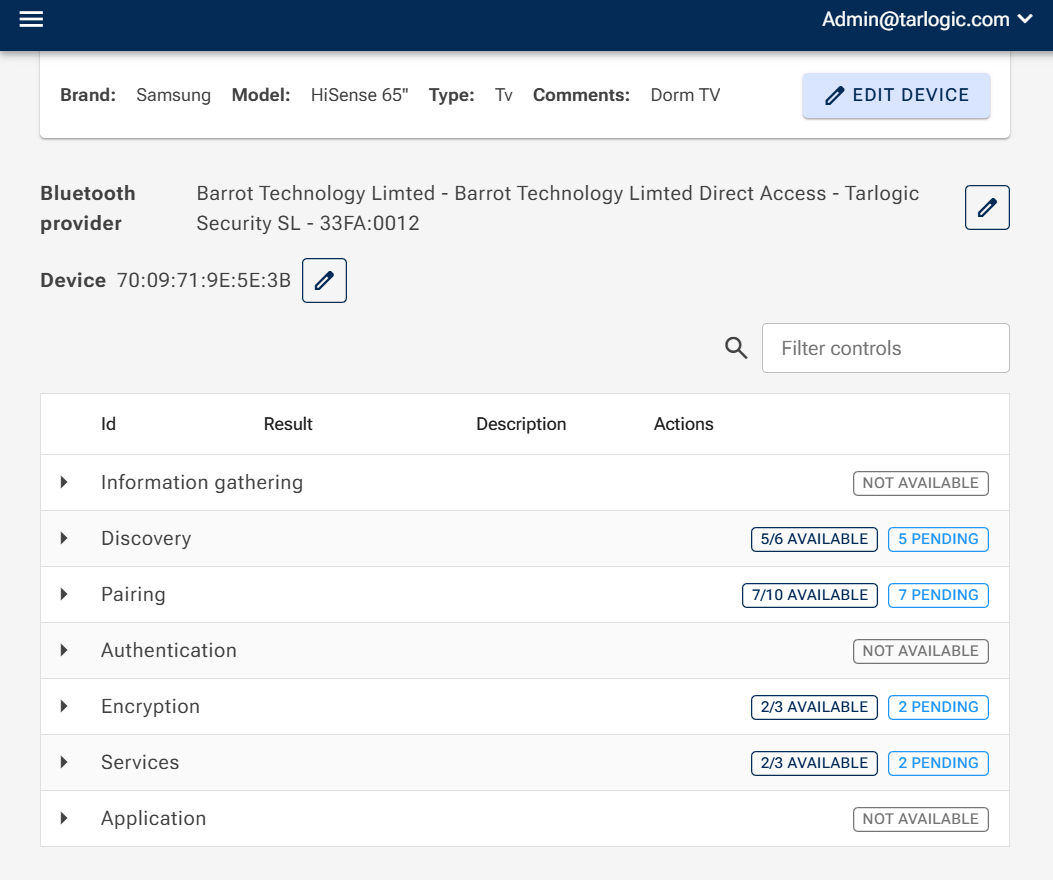
BSAM Checker
BSAM Checker is a free tool that automatically detects security and privacy vulnerabilities in Bluetooth devices.
Developed by Tarlogic's Innovation team, it automates the security tests defined in the BSAM (Bluetooth Security Assessment Methodology) to identify weaknesses that could be exploited by cybercriminals, such as tracking users or assets, intercepting communications, accessing sensitive information, or stealing high-value equipment.
With just a computer and a Bluetooth dongle, any organization or user can:
- Evaluate the security of connected devices in corporate environments.
- Check whether home devices such as headphones or wearables have vulnerabilities.
- Analyze the behavior of Bluetooth devices during security research or investigations.
- Detect vulnerabilities in critical environments, such as those relying on medical, industrial, or transportation devices.
BSAM Checker Features
This software minimizes Bluetooth device exposure by rapidly assessing the main security controls.
- Automated security controls
- Fast and easy evaluation
- 100% free tool designed to strengthen the security of the Bluetooth ecosystem
- Privacy risk identification
- Detection of insecure configurations, such as unauthenticated pairing.
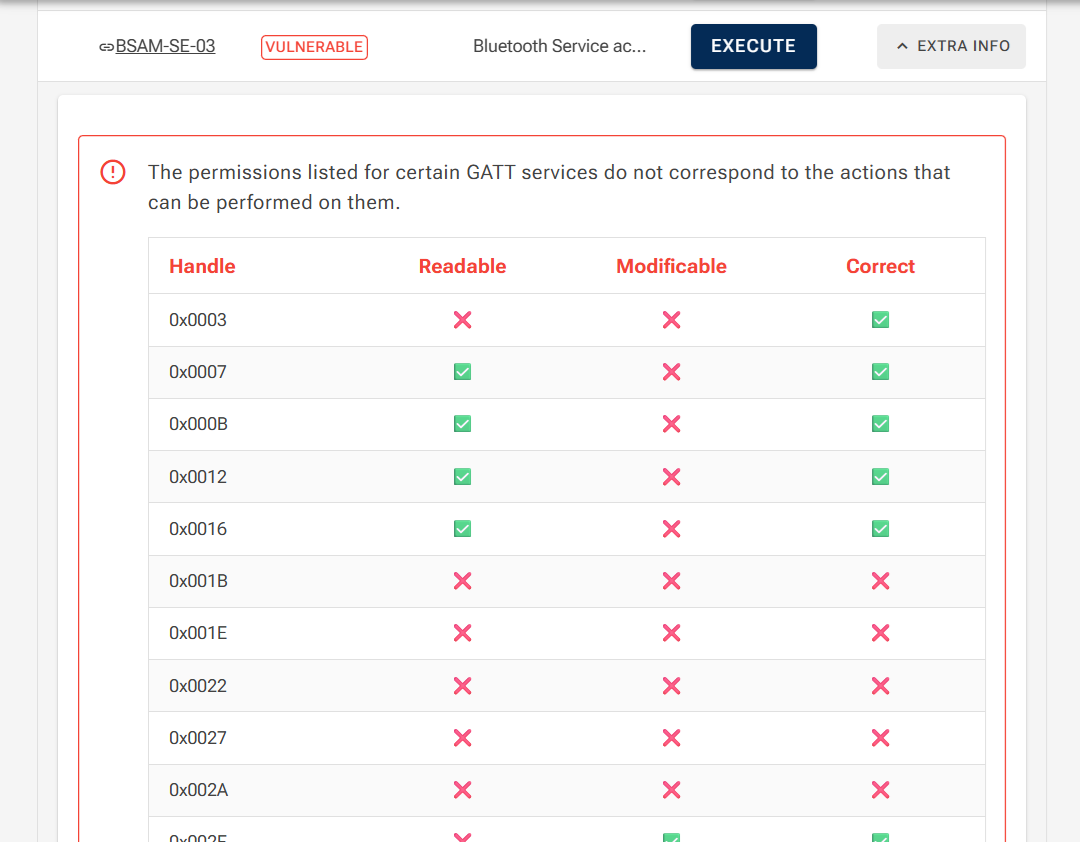
- GATT services evaluation.
- No advanced cybersecurity knowledge required
How BSAM Checker Works
BSAM Checker automates the main controls defined in the BSAM methodology to analyze the security of Bluetooth devices while helping ensure compliance with applicable regulations.
The process is simple:
-
Environment scanning
The tool detects Bluetooth devices available in the surrounding environment.
-
Identification and enumeration
Relevant device characteristics are identified, such as MAC addresses, public device names, and available services.
-
Security control execution
Automated tests are performed to detect:
- insecure configurations
- privacy issues
- exploitable vulnerabilities
-
Results report
The user receives information about detected risks and potential attack vectors.
