
Cyber for all - Page 7
This blog is a windows on a complex world. An overlook to the universe of technology which drives our daily life, using a divulgative and enjoyable perspective
Industrial cyber espionage and theft of business secrets
Industrial cyber espionage and the theft of strategic information can lead to huge economic losses and damage to companies’ competitiveness At the end of December 2023, Akira[...]
Read more
The Risks of Using Generative AI in Business: Protect Your Secrets
Companies developing AI systems and those contracting third-party applications should know the risks of using generative AI in business 2023 was the year that generative AI went ma[...]
Read more
How do you test a company’s cybersecurity?
Continuously testing a company’s cybersecurity is essential to ensuring business continuity and preventing a cyber-attack from causing significant damage A few days ago, ther[...]
Read more
The 16 types of malware used by criminals
Viruses, Trojans, spyware, ransomware… the types of malware used by malicious actors have multiplied and become more sophisticated Ransomware to extort money from companies a[...]
Read more
How do you detect vulnerabilities in applications?
Security audits are essential to detect vulnerabilities in web and mobile applications before they are exploited. Just this February, the National Institute of Standards and Techno[...]
Read more
OWASP: Top 10 Mobile Application Risks
The OWASP Top 10 Mobile Application Risks includes the most critical vulnerabilities that criminals can exploit As the saying goes, good things come to those who wait. Eight years [...]
Read more
Tips to avoid becoming a victim of CEO fraud and other impersonation attempts
To avoid becoming a victim of CEO fraud, be wary of any suspicious communication ordering a transfer or disclosing information. 38 million euros. This was the haul made by a Franco[...]
Read more
Cyber-attacks against the education sector. When criminals go to university
Cyber-attacks against the education sector can paralyse universities and research centres and lead to personal data and intellectual property theft In mid-June, right at the end of[...]
Read more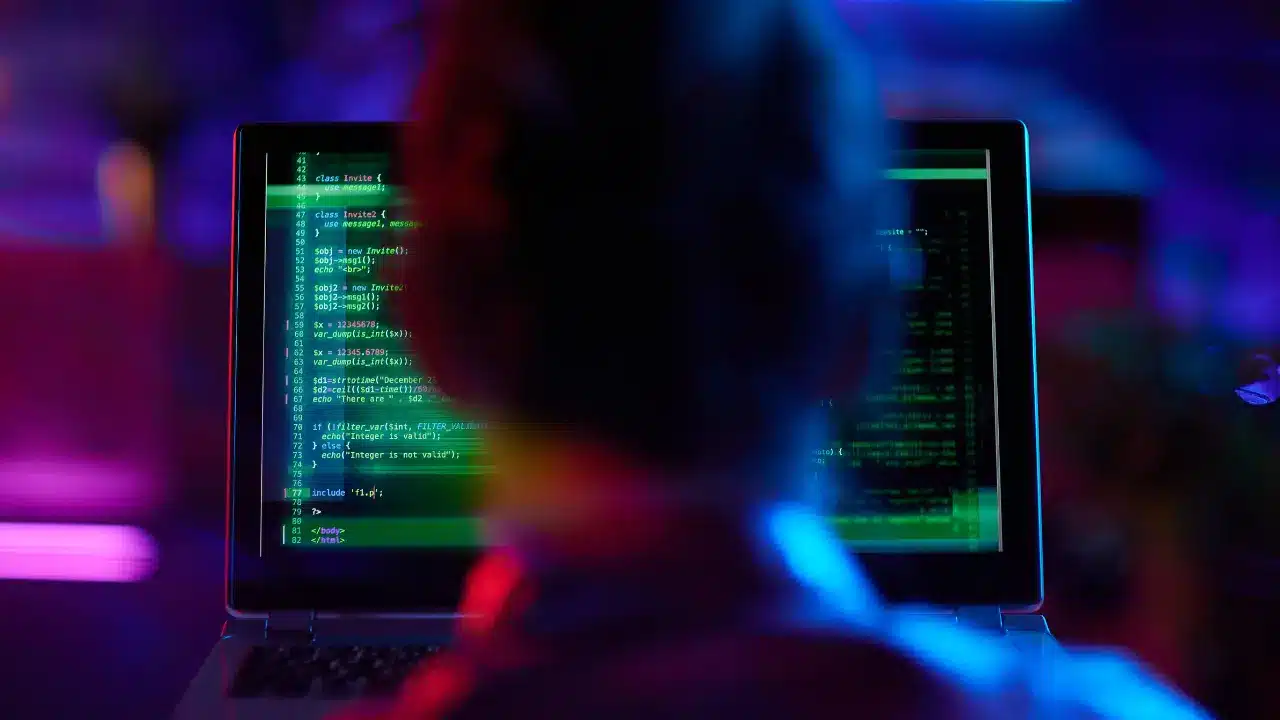
Responding to a cyber-attack in less than 1 hour
Readiness Assessment is a proactive Incident Response task that allows you to respond to a cyber-attack in minutes and minimize its impact 49 million dollars. That’s how much[...]
Read more
Cryptocurrency fraud, social media hacking, malware, and AI
Social media hacking, crypto drainers and malicious use of generative AIs are enabling criminals to commit more sophisticated cryptocurrency frauds 2024 has started with turbulence[...]
Read more